This week I got a text that there was a new sign-in device detected on my Coinbase account that was not recognized; and if it wasn’t me that I should click to update my info on a TinyURL that was so kindly inserted into the text message. Clearly a phishing scam, because I do not have a Coinbase account. The text was perfectly timed, as March is Fraud Prevention Month #FPM2022. The Canadian Anti-Fraud Centre (CAFC) reported $380 million in financial fraud losses last year. With over 100,000 reports of fraud last year, there is a good chance you have been targeted and may not even have realized. Most people ignore them and go about their day, but many fall victim to scams and fraud. Scammers speak to our fears and wants and target the well meaning, like some of the prominent scams today, eg: the taxi scam, the grandparent scam or even the fake Interac e-transfer. They make the news because if we are equipped with knowledge, we can be smarter and exert some control in avoiding them. But what about the 85% of unreported fraud, or the fraud that we can’t have control over, specifically in the payment processing space?
Fraud impacts consumers and businesses alike
According to the Canadian Federation of Independent Business (CFIB), one in every five businesses have been victim to fraud, with losses averaging in excess of $6000.
With the number of credit and debit cards in circulation growing by 2 billion between 2019 and 2021, the most common fraud is credit and debit card fraud. While the use of payment cards has benefited businesses and consumers, with this convenience came many losses from fraudulent use.
Fraudulent card uses fall into two main categories: lost/stolen cards used in unauthorized transactions, and counterfeit cards illegally produced and purchased.
Historically, and to this day, fraudsters utilize skimming devices. Skimming is the process of capturing cardholder information from the magnetic stripe of a credit or debit card at the point-of-sale terminal or ATM, and transferring it to another card for further fraudulent use. However, with the introduction of secure EMV chip technology, there has been a downward trend in this type of fraud. With the fraudsters now being disrupted in their execution of fraud, they turn to the underworld and black-market of fraudulent cards being sold online. The validity of these cards is then tested (known as auth testing) using an automated bot or script run on an open payment page online. They are able to run hundreds of transactions within seconds, and leave behind the impact of disputes from stolen cards and fees from the authorizations and declines.
The new facet of fraud
Fraudsters are in the business of making money as quickly as possible, as much as possible, and with the least amount of work. With this, their tactics are evolving and shifting to debit and purchase return fraud.
Debit cards that are run through network partners like Interac in Canada and Maestro in the US, offer merchants a cost-effective payment acceptance, and offer cardholders instantaneous access to their funds in the event of a returned product and issuance of a refund. This is in comparison with credit card returns, where the cardholder will often only see their refunds within 7 to 10 business days. Roughly 9% of in store sales are refunded, and with 29.9 million debit cards circulating just four years ago, and steadily growing, businesses are adjusting their refund limits to accommodate their debit card customers.
Businesses are told that chip enabled cards are safe and shift liability, and because debit card transactions are not alarming, they often go unnoticed. As expected, fraudsters saw an opportunity to exploit — and this new facet of fraud offers no protection.
From stolen credit cards to stolen payment terminals
Credit card terminal (pin pad) thefts themselves are not new – a quick news search will reveal this is an ongoing issue. What has evolved is how these stolen debit machines are utilized. In previous years, point-of-sale terminals were stolen to be fitted with skimming devices to steal credit card data, now the payment terminals are being stolen to perform return fraud. This occurs in two stages – first, the stolen terminals are being used to attempt refunds from the impacted merchant to counterfeit prepaid or Interac debit cards (bank cards), which are then used to make purchases elsewhere or cashed out at an ATM. The fraudsters will attempt to refund the maximum the merchant’s account will allow depending on the refund limits they have set, and with instantaneous debit refunds the consequences to the merchant can be devastating. Equipped with industry know-how and a successful money maker (the credit card terminal), that has a direct connection to a business’s bank account, the fraudsters move on to wreak havoc nationwide by a phenomenon referred to as pin debit intrusion. By gaining access to information and executing code, they use the stolen terminal to breach or clone other merchants’ terminals, and use the terminal they are in possession of just as if they are those merchants, effectively now having access to many accounts and the opportunity to continue issuing instantaneous refunds to themselves.
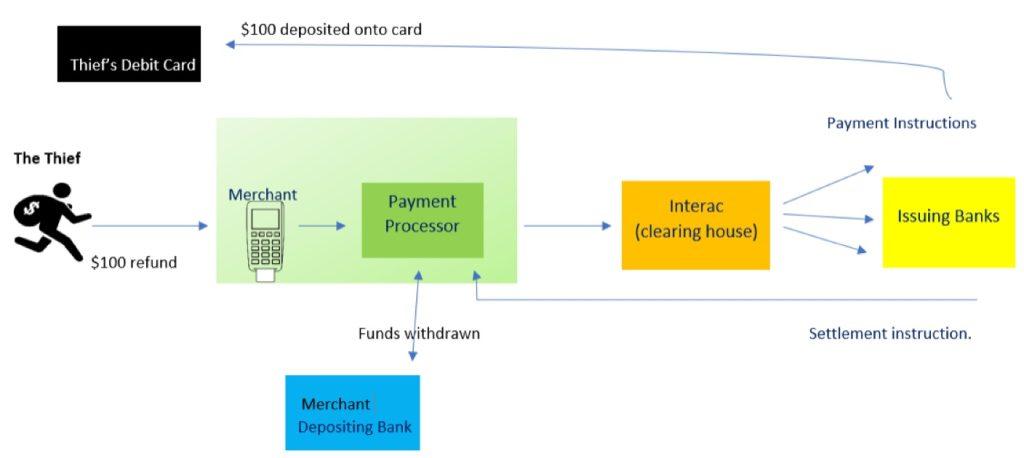
Who pays? It is not the thieves. In the normal course of business, debit refunds flow from the point-of-sale device to the payment processor, then passed to card networks and to the card issuing bank which funds the cardholder’s account instantaneously from their treasury. The payment processor is just a messenger, and the card brands and networks are only a clearing house – that leaves either the merchant or the card issuer on the hook for what can be thousands in stolen funds.
Bottom line – your credit card terminal has a direct link to your bank account and should be treated like cash.
What can we do?
Fraud is performed by groups as well as individuals who together form a network of organized crime. By working together in fighting fraud, businesses can build a stronger network with a greater defense against payment processing fraud.
As a business ourselves and your payment partner, Cartis Payments is dedicated to fraud prevention. Here are our top tips in fighting the different facets of credit card processing fraud:
- Protecting your credit / debit card terminal:
- Keep track of terminal serial numbers
- Monitor cameras and examine the device daily for any tampering or swapped out units
- Don’t leave payment terminals unattended with cardholders
- Secure / tether the device
- Watch for staff distraction tactics during a transaction
- Immediately report stolen terminals to your payment processing provider and file a police report
- Terminals that are no longer in use should be returned to the payment processor to be wiped out.
- If you own your payment terminal and wish to sell it, be mindful of who you sell it to and make sure your terminal file has been deleted.
- Preventing return fraud:
- Request default terminal passwords to be changed and lock refunds and security menu with the password
- Create separate employee passwords
- Never keep passwords written down
- Set debit refund limits
- Preventing auth testing:
- Set daily, hourly and IP velocity fraud filters
- Enable CAPTCHA
- Enable a login to the payment page
- Preventing Card Not Present (CNP) / eCommerce fraud:
- Trust your instincts on large telephone orders or where orders are asked to be shipped to a different address.
- If you are unsure if a card is fraudulent, call the auth center with a Code 10.
- Keep records of correspondence and cardholder information
- Monitor for compromised website and perform malware scans
- Enable custom rules to validate CVV / AVS matches
- Sign up for our fraud chargeback prevention tools
- Best practice guidelines
- Don’t allow cardholders to key in cards on the payment terminal
- Run cards as chip and pin on the payment terminal
- Don’t reattempt a card that declined twice
- Don’t reattempt a card that comes back with “Pick Up Card” response code
- If you use a software, have them work with us to integrate to the terminal to streamline transactions, reduce errors and prevent fraud by limiting refunds only to cards used for the original sale.
In addition to these tips, our merchants can utilize our complimentary reporting tool, My Payments Insider, to monitor authorizations for unfamiliar or suspicious transactions.
It’s time to swipe back! We’re in this together, contact us to share your stories and tips against payment processing fraud.

